Ubuntu users worldwide are experiencing widespread service disruptions after hacktivists launched a sustained distributed denial-of-service attack against Canonical’s infrastructure. The attack has been ongoing for approximately 20 hours, preventing users from updating their systems and accessing critical security services.
The Islamic Cyber Resistance in Iraq 313 Team claimed responsibility for the attack on their Telegram channel. Canonical acknowledged the situation on its website, stating that its “web infrastructure is under a sustained, cross-border attack” and that the company is working to address it.
The timing of this attack is particularly concerning for the Linux community. Ubuntu is one of the most popular Linux distributions, used by millions of developers, businesses, and individual users worldwide. When security updates can’t be installed, systems become vulnerable to other threats, creating a cascading security risk across the entire ecosystem.
The hacktivists used a DDoS-for-hire service called Beamed to flood Canonical’s servers with junk traffic. These “booter” services allow anyone to launch sophisticated attacks without technical expertise, democratizing cybercrime in troubling ways. The service allegedly powers attacks exceeding 3.5 Tbps – roughly half the size of what Cloudflare called the largest DDoS attack ever recorded.
Several critical Ubuntu services are affected by the ongoing attack:
- Ubuntu’s security API, which handles system updates
- Package installation services
- Multiple Ubuntu and Canonical websites
- Community forums and documentation sites
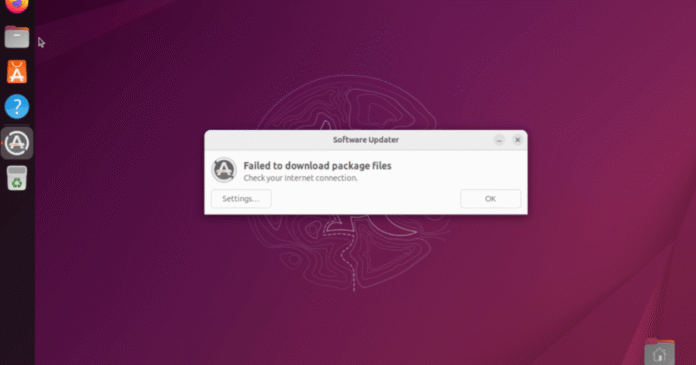
TechCrunch confirmed the impact by testing updates on Ubuntu devices, which failed to install during the attack window. Ubuntu developers have been coordinating response efforts through unofficial community forums, highlighting how the attack has disrupted normal communication channels.
This incident shows how easily critical open-source infrastructure can be disrupted by relatively unsophisticated attacks. While DDoS attacks are crude compared to advanced persistent threats, they remain effective because they exploit the fundamental architecture of the internet itself. When legitimate traffic can’t reach servers, even the most secure systems become unusable.
The rise of DDoS-for-hire services has made these attacks more accessible and affordable for bad actors. Law enforcement agencies including the FBI and Europol have been playing an ongoing game of cat and mouse with these services, regularly seizing domains and making arrests. However, new services continue to emerge as quickly as old ones are shut down.
For Ubuntu users, this attack serves as a reminder of how dependent modern computing has become on centralized update servers. Unlike some other Linux distributions that offer multiple mirror sites for redundancy, Ubuntu’s architecture creates single points of failure that can be exploited by attackers.
Canonical spokesperson Lelanie de Roubaix confirmed the company’s earlier statement but did not provide additional details about when services might be restored or what specific measures are being taken to mitigate the attack.
